How to protect your business against cyber crime
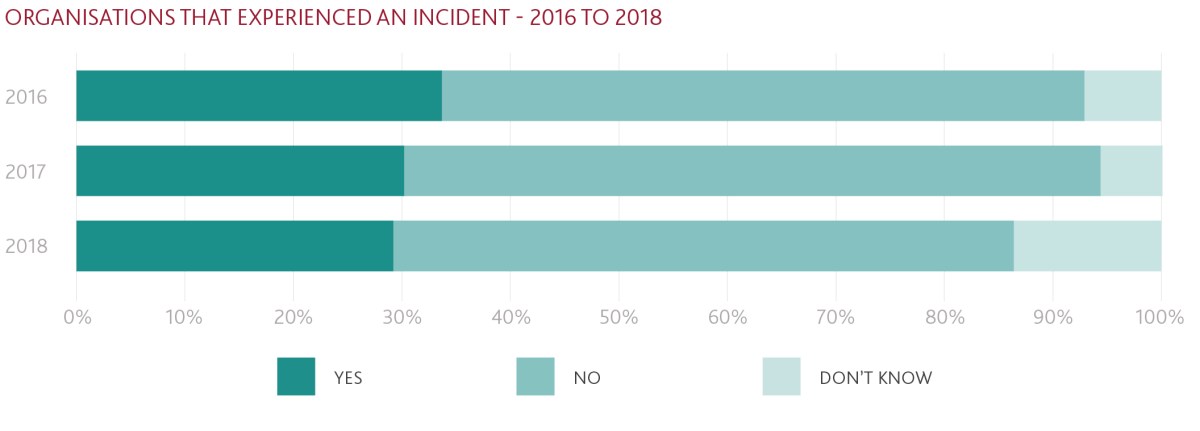
Small businesses need to be more vigilant against hackers than ever before in the wake of a new report that shows cyber crime is on the rise.

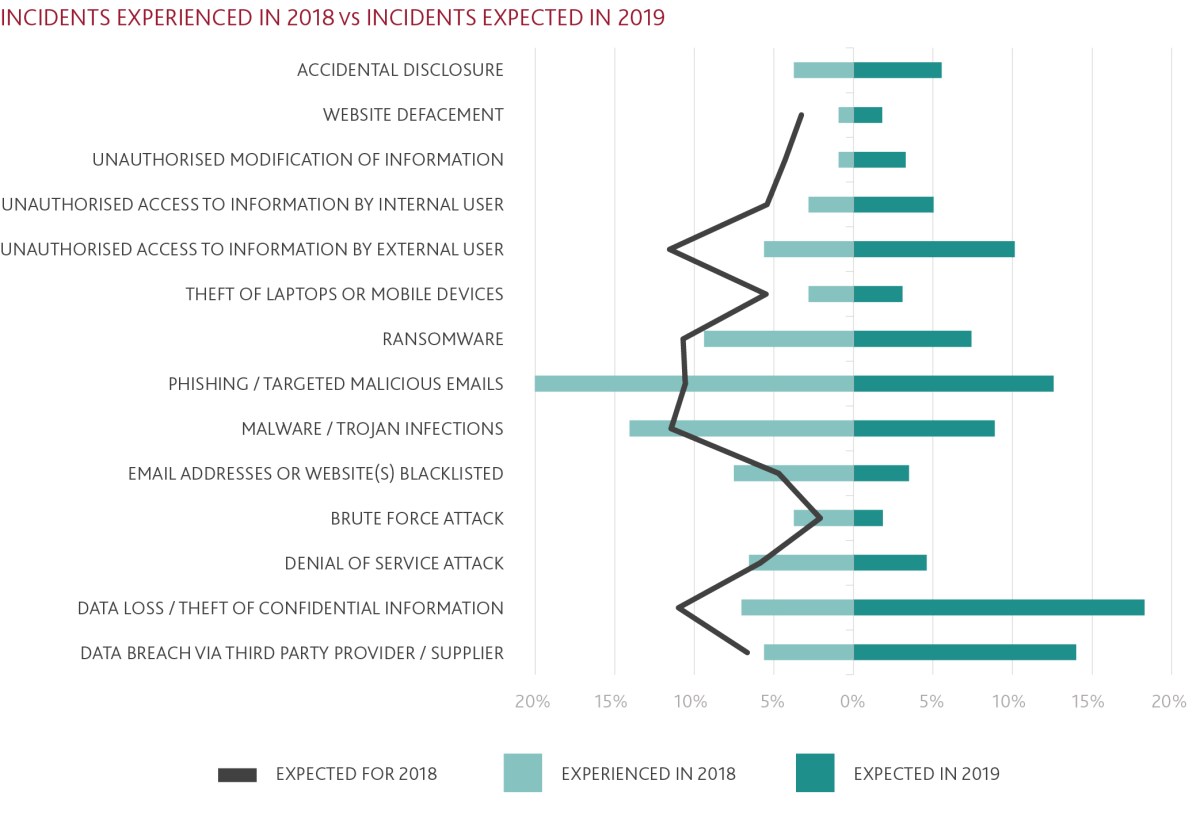
The 2018/2019 BDO and AusCERT Cyber Security Survey found data loss/theft of confidential information incidents rose by 78.68 per cent in 2018 compared to 2017.
While this could be partially explained by the February 2018 introduction of mandatory reporting through the Notifiable Data Breaches (NDB) scheme, BDO Technology Advisory Partner Nick Kervin said cyber attacks continued to increase across the board and were changing in their form.
The survey also found that respondents demonstrated a growing awareness of cyber security issues in 2018 but were still not focusing enough on response or incident management procedures.
Kervin said as businesses became more aware and savvy in some areas, the criminals used different approaches to hack an organisation’s information.
“Ten years ago it was all about getting the right firewall in place and that forced the criminals to take a different approach to try to get access to information or redirect funds,” he said.
“It’s very similar to securing your house – they’ll look at your defences to work out your weakness then they’ll work out the effort required and the potential pay off to determine if they will break in.
“If organisations approach it in that respect then that will help them think about different ways to ensure they are secure rather than just making sure there are strong locks on the door.
“If you’ve got very tight defences across your whole house or your whole business then they are going to potentially move on to someone who hasn’t.”
Under the Notifiable Data Breach (NDB) scheme, agencies and organisations are obliged to report data breaches to the Office of the Australian Information Commissioner (OAIC) and affected individuals.
A data breach occurs when personal information held by an organisation is lost or subjected to unauthorised access or disclosure.
One of the most common methods cyber criminals use to steal money from business is to hack into email systems, tracking invoices, redirecting payments to fraudulent bank accounts.
Hacked email accounts can also be used by cyber criminals to send notices to suppliers advising a change of bank details, directing payments to bogus accounts.
“It seems to be a very common incident that we’re seeing so businesses need to be thinking about their internal processes to mitigate the risk that somebody gets in there and changes the bank account details,” Kervin said.
“Businesses have become so reliant on electronic communications and emails but those systems are susceptible to being breached or compromised so a lot of small businesses need to put in some old fashioned control points where they pick up the phone and speak to someone to confirm that something has changed.
“Otherwise it’s very easy for someone to doctor up an invoice, change the bank account details on the bottom and all of a sudden the money has been redirected and by the time you realise the money is gone.”
Kervin said many small businesses relied on their managed internet service provider to look after their cyber security but this did not make them immune to cyber attacks.
He said the managed internet service providers themselves were also becoming popular targets for cyber criminals.
“That’s important for small businesses to understand: not only do they need to look at their own defences but they should also be keeping an eye on how well their managed service provider is keeping up to date with the latest in cyber security,” he said.
“There seems to be a common approach by the cyber crims out there that rather than going for each individual small business, if they go for the managed services provider it could give them access to a whole bunch of businesses.”
The Australian Signals Directorate (ASD) launched the ‘Essential Eight’, which is a suite of mitigation strategies to bolster cyber security and to reduce the impact if you do have an incident. It was launched by the Australian Government in February 2017, 12 months before the NDB scheme began.
Kervin said having a good look at the ASD’s Essential Eight was essential for all small business owners.
He said small businesses needed to also appreciate the importance of a two-factor authentication process for securing email accounts.
“In my conversations over the past 12 months I’ve been directing people to have a look at the ASD’s Essential Eight, understand them and ask their managed service provider how they are being applied to the client’s organisation and also what the managed service provider’s maturity is with the ASD Essential Eight and other cyber security defences,” he said.




